Aviation Safety - Presentation Demo¶
Aletheia is a GraphRAG platform designed for domain-specific analytical reasoning over knowledge graphs.
It provides the following capabilities:
- Data Ingestion across multiple domain-specific knowledge graphs
- Schema inference mechanisms based on LLMs and Ontologies
- Entities and Relationships Extraction, normalization and deduplication
- Hybrid search: Graph traversal plus semantic embeddings
- Temporal relationships
- Embedded ontology access for domain-aware reasoning
- Direct Cypher analytics with validation and sanitization
- Cross-graph reasoning across independent knowledge domains
- MCP connectors with self-describing, schema-aware tool interfaces
A. Why Safety Analysts Need Every Detail¶
The Swiss Cheese Model¶
Aviation safety operates on a fundamental principle: accidents don't happen because of a single failure. James Reason's Swiss Cheese Model explains how accidents occur in complex systems through the alignment of multiple weaknesses.
HAZARD
│
▼
┌───────────────┐
│ ░░░░░░░░░ │ ← Layer 1: Procedures
│ ░░░░░ ░░░░░░ │ (hole: outdated checklist)
└───────────────┘
│
▼
┌───────────────┐
│ ░░░░░░░░░░░ │ ← Layer 2: Technology
│ ░░░░ ░░░░░░░ │ (hole: sensor calibration)
└───────────────┘
│
▼
┌───────────────┐
│ ░░░░░░░░░ │ ← Layer 3: Training
│ ░░░░░░░ ░░░░ │ (hole: CRM gap)
└───────────────┘
│
▼
⚠️ ACCIDENT
(when holes align)
Each "slice of cheese" represents a defense layer (procedures, technology, training, supervision), and the "holes" are inherent weaknesses. An accident occurs only when holes in multiple layers align, allowing a hazard to traverse the entire system.
| Component | Description |
|---|---|
| Defense Layers | Barriers like regulations, equipment, training, supervision |
| Holes (Weaknesses) | Human errors, technical failures, design flaws |
| Active Failures | Direct actions that trigger events (e.g., skipping a checklist item) |
| Latent Failures | Deep systemic defects waiting to be activated (e.g., poorly designed procedure) |
Systemic Thinking
The model shifts focus from individual blame to systemic analysis. Errors are symptoms of deeper organizational and technical weaknesses that must be identified to prevent recurrence.
Why This Matters for GraphRAG¶
Safety analysts investigating incidents need to:
- Trace causal chains — From latent conditions through active failures to the accident
- Identify contributing factors — Weather, human factors, maintenance, equipment
- Connect related incidents — Similar failures across different contexts
- Find patterns — Recurring weaknesses in defense layers
This requires navigating relationships across multiple entities — exactly what GraphRAG enables. A simple keyword search cannot connect a maintenance procedure gap in Lyon with a similar QA failure in Palma de Mallorca. A knowledge graph can.
B. Why GraphRAG and not RAG?¶
RAG (Vector stores) allow AI to find conceptually similar information through embeddings: keyword search on steroids. Vector search measures proximity in semantic meaning, not structure or causality.
RAG is fast, scalable, and excellent for recall, but it doesn't understand relationships. RAG can tell you what looks alike, not what belongs together.
The Need for Structure
To move beyond pure semantic retrieval, AI needs a structured representation of meaning.
A way to connect facts, follow relationships, and reason across them.
That's where Knowledge Graphs come in.
C. Introducing EASA ECCAIRS for Aviation Safety¶
ECCAIRS (European Coordination Centre for Accident and Incident Reporting Systems) is the European framework used to collect, manage, and analyze aviation safety occurrences.
It covers:
- Standardized procedures for reporting incidents by aviation stakeholders
- Centralized and consolidated occurrence database where reports are stored and shared
- Common aviation safety taxonomy that structures how events, causes, and contributing factors are described
Together, these elements ensure consistency, comparability, and regulatory alignment in safety data across Europe.
What is an Occurrence?¶
An occurrence is the formal record of any aviation safety-related incident or event. It combines:
| Component | Description |
|---|---|
| Structured section | Based on the ECCAIRS taxonomy - encodes factual data such as event type, phases of flight, actors, and contributing factors |
| Narrative section | Free-text written in natural human language describing what actually happened, sometimes in different languages |
Together, the structured data enables large-scale analysis and comparability, while the narrative preserves context, nuance, and operational detail that cannot be fully captured by predefined fields.
Domain Complexity
Aviation safety occurrences form a highly specialized niche domain, characterized by dense technical language, extensive use of acronyms, and domain-specific jargon rooted in operations, engineering, and regulation.
D. ECCAIRS Ontology¶
Although it is published as a taxonomy rather than a formal ontology, the ECCAIRS model can be directly transformed into an ontology that describes the aviation safety domain.
It defines core domain concepts such as:
- Occurrence
- Runway
- Aircraft
- Engine
- Flight Crew Member
- Aerodrome
The resulting ontology represents a highly specialized domain vocabulary, using precise and formal terminology. For instance, Aerodrome is the canonical term covering airports, heliports, and other landing areas, reflecting the regulatory need for unambiguous and standardized language.
E. Occurrence Dataset¶
Given that the ECCAIRS occurrence database is not publicly available, this use case is built using synthetic but realistic incident data.
The current dataset contains 10 safety incidents.
The sample documents are modeled as aviation safety occurrence reports, combining structured, taxonomy-aligned fields (metadata, aircraft, flight phase, weather, findings, and recommendations) with a free-text narrative describing what happened in operational terms.
Sample Document¶
Incident Report 2024-0856-EU
Metadata
| Field | Value |
|---|---|
| Incident ID | 2024-0856-EU |
| Date | 2024-11-25 |
| Time | 19:33 UTC |
| Location | Barcelona-El Prat Airport (LEBL) |
| Country | Spain |
| Flight Phase | Cruise / En route |
Aircraft
| Field | Value |
|---|---|
| Type | Boeing 787-9 |
| Registration | EC-NBM |
| Operator | Air Europa |
Incident Description
Durante el vuelo de crucero a FL390 sobre el Mediterráneo occidental, aproximadamente 120 nm al este de Barcelona, la tripulación detectó un olor inusual a humo eléctrico en la cabina de vuelo. El comandante ordenó inmediatamente el uso de máscaras de oxígeno y declaró una emergencia (MAYDAY).
Se ejecutó el procedimiento de humo/fuego/vapores del QRH (Quick Reference Handbook). La tripulación identificó que el olor provenía del sistema de entretenimiento a bordo (IFE) en la cabina. El sistema IFE fue desactivado y el olor cesó gradualmente.
Findings
- Primary Cause: Cortocircuito eléctrico en la unidad de distribución de energía del sistema IFE
- Contributing Factors: Aging electrical components, possible moisture ingress
- Human Factors: Correct application of emergency procedures by flight crew
F. The Challenge¶
The challenge for Aletheia is to generate accurate answers given the combined characteristics of both the input data and the questions.
Data Challenges¶
| Aspect | Challenges |
|---|---|
| Both | Multiple languages, typos, abbreviations, inconsistent phrasing, highly technical aviation jargon |
| Input Data | Combines structured and unstructured information, may not align with ECCAIRS ontology (e.g., airport vs. aerodrome) |
| Questions | Can be ambiguous (e.g., referring to cities instead of aerodromes), may require multi-hop or temporal reasoning |
Example Query¶
A question such as "What incidents in Barcelona or Madrid involved Boeing aircraft and resulted in emergency declarations (MAYDAY or PAN-PAN)?" must resolve to a single incident matching all criteria:
| Field | Value |
|---|---|
| Location | Barcelona-El Prat Airport (LEBL) |
| Date | 2024-11-25 |
| Aircraft | Boeing 787-9 (EC-NBM) |
| Operator | Air Europa |
| Emergency | MAYDAY declared |
| Cause | Electrical short circuit in IFE power distribution unit |
| Outcome | Diverted to Barcelona, emergency landing, no injuries |
The Madrid incident (2024-0734-EU) involved an Airbus A330-200, not Boeing, so it doesn't match.
G. The Knowledge Graphs¶
Aletheia's aviation safety use case spans three independent knowledge graphs, each built from different data sources and covering a distinct regulatory domain.
Three Domains, One Analytical Platform¶
| Graph | Domain | Source | Purpose |
|---|---|---|---|
| Aviation Safety | 2024 European occurrences | Synthetic ECCAIRS-style reports | What happened — incidents, aircraft, operators, locations |
| Safety Recommendations | EASA Safety Recommendations | EASA SR database | What was recommended — investigation findings and corrective actions |
| Airworthiness Directives | EASA Airworthiness Directives | EASA AD database | What was mandated — mandatory inspections, modifications, and operational limits |
These three datasets mirror the real-world safety lifecycle: an incident triggers an investigation that produces recommendations, which may escalate to mandatory directives. In practice, analysts must cross-reference these databases manually. Aletheia connects them through knowledge graphs.
No Pre-Built Links
The three knowledge graphs are built independently from separate data sources. There are no pre-built cross-references between them. Aletheia bridges the gaps through entity resolution, semantic search, and ontology-informed reasoning at query time.
Aviation Safety Graph¶
10 European aviation occurrences from 2024, with multilingual narratives (English, French, Spanish).
Entities:
| Type | Count |
|---|---|
| Occurrence | 10 |
| Aircraft | 10 |
| AerodromeGeneral | 9 |
| Operator | 9 |
| Manufacturer | 6 |
| Country | 5 |
Relationships:
| Relationship | Description | Count |
|---|---|---|
| INVOLVED_AIRCRAFT | Occurrence → Aircraft | 9 |
| OCCURRED_AT | Occurrence → Aerodrome | 10 |
| LOCATED_IN | Aerodrome → Country | 10 |
| OPERATED_BY | Aircraft → Operator | 10 |
| MANUFACTURED_BY | Aircraft → Manufacturer | 10 |
Safety Recommendations Graph¶
94 EASA Safety Recommendations linked to 138 occurrences, issued by 37 investigation authorities across 24 countries.
Entities:
| Type | Count |
|---|---|
| Occurrence | 138 |
| Aircraft | 237 |
| SafetyRecommendation | 94 |
| Manufacturer | 59 |
| SafetyInvestigationAuthority | 37 |
| Country | 24 |
Relationships:
| Relationship | Description | Count |
|---|---|---|
| STEMS_FROM | SafetyRecommendation → Occurrence | 242 |
| ISSUES | SafetyInvestigationAuthority → SafetyRecommendation | 158 |
| INVOLVES | Occurrence → Aircraft | 147 |
| LOCATES | SafetyInvestigationAuthority → Country | 137 |
| MANUFACTURES | Manufacturer → Aircraft | 131 |
Airworthiness Directives Graph¶
743 EASA Airworthiness Directives covering 331 aircraft types, referencing 228 technical documents, approved by 137 design approval holders.
Entities:
| Type | Count |
|---|---|
| AirworthinessDirective | 743 |
| AircraftType | 331 |
| Document | 228 |
| DesignApprovalHolder | 137 |
Relationships:
| Relationship | Description | Count |
|---|---|---|
| APPROVED_BY | AirworthinessDirective → DesignApprovalHolder | 759 |
| APPLIES_TO | AirworthinessDirective → AircraftType | 677 |
| REFERENCES | AirworthinessDirective → Document | 199 |
| SUPERSEDES | AirworthinessDirective → AirworthinessDirective | 81 |
Scale
Combined, the three graphs contain over 2,000 entities and 5,000+ typed relationships. The Airworthiness Directives graph alone is larger than many production GraphRAG deployments.
Knowledge Graph Visualization¶
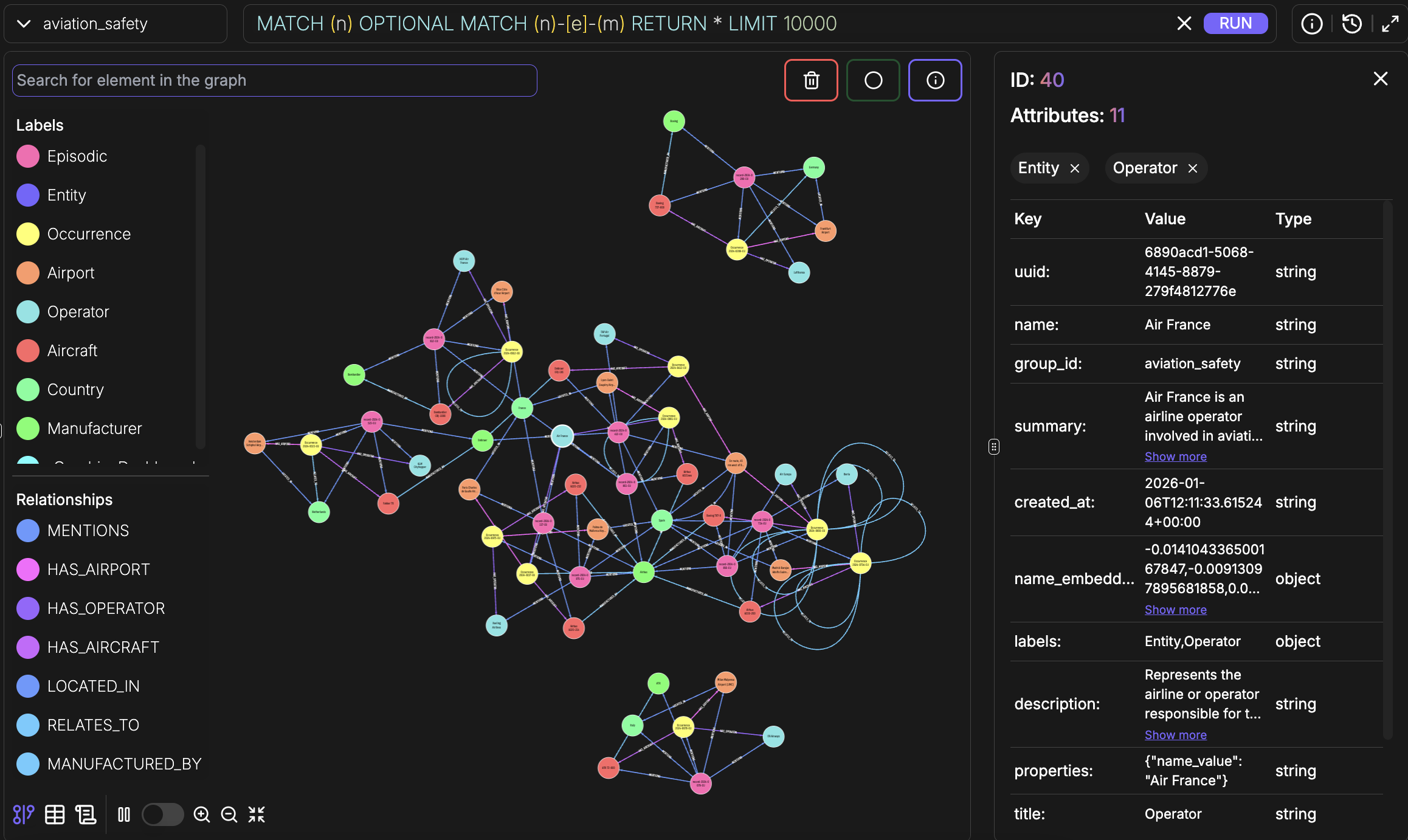
FalkorDB Graph Explorer¶
H. Building the Knowledge Graphs¶
When building a knowledge graph, an LLM is used to extract entities and relationships from text.
Without schema guidance, this process easily leads to inconsistent entity types, ambiguous relationships, and fragmented vocabularies, resulting in a graph that lacks structural coherence.
Why Schema Matters¶
| Benefit | Description |
|---|---|
| Type consistency | Identical concepts use the same canonical types |
| Relationship clarity | Relationships follow a clear, queryable vocabulary |
| Property standardization | Attributes are named consistently across entities |
| Improved retrieval | Queries reliably return all relevant results |
Schema Inference in Aletheia¶
Schema inference determines the vocabulary of entity types, relationships, and properties that the LLM must use during extraction.
The most robust approach combines LLM-assisted schema inference with domain ontologies. In this model:
- LLM-driven schema discovery
- Semantic alignment with existing ontology through knowledge graph search and embeddings
- Automatic resolution of terminology mismatches
This hybrid approach enables the extraction of high-confidence schemas, enriched and constrained by authoritative domain knowledge.
Inferred Schemas¶
Each knowledge graph has its own domain-specific schema, inferred through the same ontology-guided process.
Aviation Safety Schema
Safety Recommendations Schema
Airworthiness Directives Schema
Ingestion Process¶
I. ECCAIRS Ontology Graph¶
Ontologies encode expert knowledge about a domain.
In the context of knowledge graphs, an ontology serves as a schema or blueprint that describes:
| Component | Description |
|---|---|
| Classes | The types of entities (e.g., Person, Organization, Aircraft) |
| Properties | Attributes of entities (e.g., name, date, location) |
| Relationships | How entities connect to each other |
| Constraints | Rules about valid combinations |
The Terminology Problem¶
Without ontology alignment, inconsistencies arise:
| User Language | Ontology Term |
|---|---|
| Airport | Aerodrome |
| Aircraft, Plane, Airplane | Aircraft |
| Operator, Airline, Carrier | Operator |
| Occurrence, Incident, Event | Occurrence |
Ontology Graph Solution¶
How can we link an entity (like airport) with the corresponding ontology class (aerodrome)?
Aletheia provides the ability to build an ontology graph — a semantic projection of a formal ontology that enables the system to access domain knowledge through embeddings and graph search.
The ontology graph is built before the knowledge graph, ensuring schema inference can rely on it.
During schema inference, when detecting an "Airport" entity, Aletheia queries the ontology graph using semantic search to find the matching canonical class ("Aerodrome").
Ontology Graph in FalkorDB¶
ECCAIRS Ontology Structure¶
Ontology in the MCP Connector
The ECCAIRS ontology graph is not just a build-time tool. Each Aletheia MCP connector provides embedded ontology access through search_ontology and explore_ontology tools, enabling the LLM to decode domain terminology at query time — directly from within any data connector.
J. The MCP Connector¶
Aletheia exposes each knowledge graph through a self-describing MCP (Model Context Protocol) connector — a standardized interface that allows any LLM to discover, search, traverse, and analyze the graph.
Each connector is domain-aware: it advertises what entity types, relationship types, and query patterns exist in its graph, enabling the LLM to generate precise queries without guessing at graph structure.
Tool Surface¶
Each connector provides 13 tools organized into five capability groups:
| Group | Tools | Purpose |
|---|---|---|
| Semantic Discovery | search, explore_node | Find entities by meaning, traverse graph neighborhoods |
| Schema & Ontology | get_schema, search_ontology, explore_ontology | Understand graph structure, decode domain terminology |
| Cypher Analytics | run_cypher | Count, aggregate, compare, compute — direct analytical queries |
| Community Intelligence | build_communities | Cluster entities, detect thematic groups |
| Data Management | add_memory, get_episodes, get_episode_context, delete_entity_edge, delete_episode, clear_graph, get_status | Ingest, inspect, maintain |
Search Capabilities¶
The search tool provides unified access to nodes, edges, and communities with advanced filtering:
| Feature | Description |
|---|---|
| Entity type filtering | Restrict results to specific types (e.g., only SafetyRecommendation entities) |
| Edge type filtering | Search for specific relationships (e.g., only STEMS_FROM edges) |
| Reranker strategies | Five ranking algorithms: reciprocal rank fusion, diversity ranking, cross-encoder precision, graph proximity, and importance ranking |
| Graph-proximity search | Bias results toward a known entity's neighborhood using center_node_uuid |
| BFS from known entities | Breadth-first graph traversal starting from specific nodes |
| Temporal filtering | Query edges valid at a specific point in time |
| Community search | Search across detected entity clusters |
Cypher Analytics¶
The run_cypher tool executes read-only Cypher queries with a four-stage validation pipeline:
LLM generates Cypher
│
▼
┌─ Stage 1: LLM Fixups ─────────────┐
│ Smart quotes, unicode, missing │
│ RETURN clause, direction fixes │
└────────────────────────────────────┘
│
▼
┌─ Stage 2: FalkorDB Dialect ────────┐
│ Auto-fix: date(), toLower, etc. │
│ Reject: APOC, pattern comp., etc. │
└────────────────────────────────────┘
│
▼
┌─ Stage 3: Security Whitelist ──────┐
│ Only: MATCH, WHERE, RETURN, WITH │
│ Reject all write operations │
└────────────────────────────────────┘
│
▼
┌─ Stage 4: Safety Injection ────────┐
│ Auto-inject LIMIT, timeout │
└────────────────────────────────────┘
│
▼
GRAPH.RO_QUERY (database-level
read-only enforcement)
Results are returned as typed JSON envelopes (scalar, tabular, graph, or path) with metadata including row count, truncation status, execution time, and a list of any auto-corrections applied to the query.
Embedded Ontology Access¶
Every data connector includes search_ontology and explore_ontology tools that query the ECCAIRS ontology directly. The LLM can decode aviation shorthand (e.g., "SCF-NP" → "System/Component Failure - Non-Powerplant", "ATA 36" → "Pneumatic system") without switching to a separate ontology server.
Self-Describing Connectors¶
Each connector advertises its domain schema in the tool metadata. For example, the Safety Recommendations connector tells the LLM:
Entity types: Aircraft, Country, Manufacturer, Occurrence,
SafetyInvestigationAuthority, SafetyRecommendation
Edge types: INVOLVES, ISSUES, LOCATES, MANUFACTURES, STEMS_FROM
This means the LLM knows — before making any query — that STEMS_FROM connects SafetyRecommendation to Occurrence, that ISSUES connects SafetyInvestigationAuthority to SafetyRecommendation, and so on. It can write precise filtered searches and valid Cypher queries on the first attempt.
Discovery + Analytics
The combination of semantic search for discovery ("find me relevant entities") and Cypher for analytics ("count, aggregate, prove") means the LLM can handle both exploratory and computational questions through the same connector.
K. Aletheia in Action¶
The demo is structured as a progressive showcase across four levels of complexity. Each level introduces new capabilities, building from semantic search over a single graph to full analytical reasoning across three knowledge graphs with ontology support.
Act 1 uses a single tool. By Act 4, the system orchestrates 10+ tool calls across four knowledge graphs in a single conversation turn.
Act 1: "It Understands"¶
Single knowledge graph (Aviation Safety). Semantic search. Goal: demonstrate that Aletheia interprets meaning, not just keywords — across languages and imprecise queries.
Q1 — Semantic cause lookup
"What caused the turbulence-related injuries near Barcelona?"
| Capability | What's being tested |
|---|---|
| Semantic understanding | "Near Barcelona" is not a stored field — the system must match this to Barcelona-El Prat Airport |
| Data fusion | The answer combines structured fields (flight phase, injuries) with narrative details |
Q2 — Multilingual entity resolution
"¿Qué fabricante construyó el avión que tuvo el incidente de humo en cabina sobre el Mediterráneo?"
| Capability | What's being tested |
|---|---|
| Multilingual support | Query is in Spanish; incident narrative is in Spanish; manufacturer entity is in English |
| Multi-hop traversal | Resolves: Spanish query → incident → aircraft → manufacturer (three hops) |
| Entity resolution | "humo en cabina sobre el Mediterráneo" must resolve to Occurrence 2024-0856-EU |
Q3 — Temporal reasoning
"What was the emergency response timeline at Palma de Mallorca during the fuel spill?"
| Capability | What's being tested |
|---|---|
| Temporal extraction | Sequencing events from narrative text: detection → response → evacuation → resolution |
| Natural language generation | Synthesizing a coherent timeline from distributed facts |
Act 1 Summary
Three questions, one graph, one tool (search). The system demonstrates semantic understanding, multilingual bridging, multi-hop entity resolution, and temporal reasoning. These are the fundamentals — and they already go beyond keyword search. But we're just getting started.
Act 2: "It Navigates"¶
Single knowledge graph, but now using the full MCP tool surface: get_schema, run_cypher, explore_node, search_ontology. Same data, dramatically more powerful questions.
Q4 — Schema-aware analytics
"Which manufacturer has the highest incident count in our data, and what types of aircraft are involved for each?"
Expected approach: The LLM calls get_schema to understand the graph topology, then writes a Cypher aggregation query:
MATCH (o:Occurrence)-[:INVOLVED_AIRCRAFT]->(a:Aircraft)-[:MANUFACTURED_BY]->(m:Manufacturer)
RETURN m.name, count(DISTINCT o) AS incidents, collect(DISTINCT a.name) AS aircraft_types
ORDER BY incidents DESC
| Capability | What's being tested |
|---|---|
| Schema awareness | The LLM discovers graph structure before querying |
| Cypher analytics | Multi-hop aggregation across three entity types — impossible with semantic search alone |
| Structured computation | The answer is computed, not retrieved |
Q5 — Graph traversal + analytical follow-up
"Show me everything connected to the Palma de Mallorca fuel spill — the aircraft, operator, airport, country, manufacturer. Then tell me if this operator has other incidents in our data."
Expected approach: explore_node("Occurrence 2024-0975-EU", depth=2) maps the full neighborhood, then a Cypher query checks for other incidents by the same operator.
| Capability | What's being tested |
|---|---|
| Graph traversal | explore_node with depth=2 reveals the complete entity neighborhood |
| Chained workflow | Discovery (explore) → analytics (Cypher) — two tools composed for a single answer |
Q6 — Ontology-informed analysis
"What ECCAIRS occurrence categories are represented in our incident data? Use the ECCAIRS ontology to classify each incident."
Expected approach: The LLM calls search_ontology to retrieve ECCAIRS Occurrence Category Values, then maps each incident's characteristics against the formal taxonomy.
| Capability | What's being tested |
|---|---|
| Embedded ontology access | The LLM queries domain definitions without switching to a separate system |
| Domain translation | Mapping free-text incident descriptions to standardized ECCAIRS categories |
Act 2 Summary
Same graph as Act 1, but the questions changed fundamentally. We moved from "find me something" to "compute this for me" and "classify this using domain knowledge." The new capabilities — schema awareness, Cypher analytics, graph traversal, chained workflows, and embedded ontology — transform a search tool into an analytical instrument.
Act 3: "It Connects"¶
Three knowledge graphs (Aviation Safety + Safety Recommendations + Airworthiness Directives). Cross-domain reasoning. Goal: show that connecting independent graphs multiplies analytical power.
Q7 — Cross-graph entity resolution
"The fuel spill at Palma de Mallorca involved a Vueling A320. Are there any active airworthiness directives for the A320 fuel system, and have any safety recommendations been issued for similar maintenance-induced fuel integrity issues?"
Expected approach:
- Aviation Safety graph: confirm the incident details — A320-232, incorrect valve torque
- AD graph: search for ADs applying to A320 fuel system (ATA 28)
- SR graph: search for recommendations related to maintenance-induced fuel integrity failures
── Aviation Safety connector ──────────────────────────────
search("Palma de Mallorca fuel spill A320")
→ Occurrence 2024-0975-EU, A320-232, Vueling, ATA 28
── Airworthiness Directives connector ─────────────────────
search("A320 fuel system", entity_types=["AirworthinessDirective"])
run_cypher("""
MATCH (ad:AirworthinessDirective)-[:APPLIES_TO]->(at:AircraftType)
WHERE at.name CONTAINS 'A320' AND ad.name CONTAINS 'fuel'
RETURN ad.name, at.name
""")
── Safety Recommendations connector ───────────────────────
search("maintenance fuel integrity failure", entity_types=["SafetyRecommendation"])
| Capability | What's being tested |
|---|---|
| Cross-graph reasoning | Three separate queries across three independent graphs |
| Entity resolution | "A320" appears in all three graphs with different naming conventions |
| Regulatory cross-referencing | Connecting an incident to both recommendations and directives |
Q8 — Manufacturer intelligence report
"Build me an Airbus risk profile: count the 2024 incidents, find any open safety recommendations for the involved aircraft types, and list active ADs. What's the combined risk picture?"
Expected approach: Cypher analytics on each graph, then cross-reference by aircraft type.
| Capability | What's being tested |
|---|---|
| Multi-graph aggregation | Cypher queries across all three graphs, correlated by manufacturer |
| Structured synthesis | Combining counts, statuses, and applicability into a coherent risk profile |
| Analytical reasoning | The answer requires judgment — which combinations signal highest risk |
Act 3 Summary
Each graph alone tells part of the story. Connected, they tell the whole story. An incident becomes a risk signal when you can trace whether it's covered by a recommendation, and whether that recommendation became a mandatory directive. The system is now doing cross-graph entity resolution, multi-graph aggregation, and regulatory lifecycle tracing.
Act 4: "It Thinks Like an Analyst"¶
Three graphs + ECCAIRS ontology as semantic backbone. Full analytical reasoning. These are questions that safety analysts actually ask — and they normally require days of manual cross-referencing.
Q9 — ECCAIRS-coded analytical query
"Any SCF-NP events with ATA 36 involvement that resulted in diversions? Cross-reference with open safety recommendations and applicable ADs."
Expected approach:
- Ontology decode:
search_ontology("SCF-NP")→ "System/Component Failure - Non-Powerplant";search_ontology("ATA 36")→ "Pneumatic system (bleed air, pressurization, ducting)" - Aviation Safety graph: search with decoded terms
- AD graph: search for ATA 36 directives → discover the dense cluster of A320-36-xxxx SBs and AD 2025-0096
- SR graph: search for open recommendations on bleed/pneumatic systems
| Capability | What's being tested |
|---|---|
| Ontology as decoder | The analyst spoke in ECCAIRS shorthand — the ontology translated it to precise search terms |
| Cross-graph correlation | Four queries across three data graphs + ontology, correlated by ATA chapter |
| Domain expertise | Without decoding SCF-NP and ATA 36, the query is opaque |
Q10 — Full safety lifecycle trace
"Trace the complete safety lifecycle for bleed duct fire risk on wide-body Airbus: start with AD 2021-0280 for the A380 bleed duct detachment issue. Did the corrective actions prevent any 2024 incidents? Do similar risks exist for A320 or A330 fleets without equivalent ADs?"
Expected approach:
- AD graph:
explore_node("AD 2021-0280", depth=2)→ map the directive, its referenced SBs, aircraft applicability - Aviation Safety graph: search for A380 bleed/pneumatic incidents in 2024 → zero results (the AD worked)
- AD graph: Cypher query for all ATA 36 ADs across Airbus types → find AD 2025-0096 (A320) and AD 2023-0136 (A330)
- Gap analysis: identify aircraft types with similar risk but no equivalent directive
| Capability | What's being tested |
|---|---|
| Lifecycle tracing | From directive → effectiveness validation → adjacent risk identification |
| Effectiveness assessment | Zero incidents = success case for the AD's corrective actions |
| Proactive risk identification | Finding unregulated risks by analogy with regulated ones |
Q11 — Predictive gap analysis
"Identify 2024 incidents whose root causes have no matching airworthiness directive. For each gap, check if a safety recommendation exists. If neither exists, flag it as an unmonitored risk."
Expected approach:
- Aviation Safety graph: Cypher to extract all incidents with their primary causes
- For each cause pattern, search the AD graph for matching directives
- Where no AD exists, search the SR graph for matching recommendations
- Where neither exists → unmonitored risk
── Aviation Safety connector ──────────────────────────────
run_cypher("""
MATCH (o:Occurrence)-[:INVOLVED_AIRCRAFT]->(a:Aircraft)
-[:MANUFACTURED_BY]->(m:Manufacturer)
RETURN o.name, a.name, m.name, o.summary
""")
→ 10 incidents with aircraft types and summaries
── For each incident, cross-reference ─────────────────────
── Airworthiness Directives connector ─────────────────────
search("<cause pattern>", entity_types=["AirworthinessDirective"])
→ AD found? ✓ Covered | No match? → check SR graph
── Safety Recommendations connector ───────────────────────
search("<cause pattern>", entity_types=["SafetyRecommendation"])
→ SR found? ⚠ Pending | No match? → 🔴 Unmonitored risk
| Capability | What's being tested |
|---|---|
| Gap detection | Computing the complement — what exists in incident data but not in directive data |
| Three-graph coverage analysis | Systematic check: incident → AD? → SR? → gap? |
| Predictive intelligence | Identifying tomorrow's directives from today's incidents |
Q12 — Predictive gap analysis (emerging risks)
"Identify emerging risks that haven't yet reached the Airworthiness Directive stage: Find 2024 incidents with novel or unusual primary causes. Check if any Safety Recommendations exist for similar issues (even if from different aircraft types). Verify that NO Airworthiness Directive currently addresses these specific failure modes. Flag these as 'regulatory gaps' requiring proactive attention. Estimate time-to-AD based on historical patterns from similar issues."
| Capability | What's being tested |
|---|---|
| Predictive safety intelligence | Identifying risks before they escalate to mandatory directives |
| Multi-graph gap analysis | Cross-referencing incidents, recommendations, and directives to find coverage gaps |
| Temporal pattern estimation | Using historical AD timelines to project when emerging risks may require regulation |
Q13 — Manufacturer intelligence (consolidated report)
"Create a consolidated Airbus safety intelligence report: List all 2024 incidents involving Airbus aircraft from Aviation Safety. Find all open Safety Recommendations mentioning Airbus or specific Airbus types. Retrieve all active Airworthiness Directives for Airbus aircraft. Identify any Airbus models appearing across all three datasets with unresolved issues. Recommend which Airbus fleet operators should prioritize based on combined risk exposure."
| Capability | What's being tested |
|---|---|
| Multi-graph aggregation | Querying all three graphs for manufacturer-specific data |
| Manufacturer-centric intelligence | Building a consolidated risk profile from incidents, recommendations, and directives |
| Risk prioritization | Combining signals across domains to recommend operator action priorities |
L. Summary¶
Capabilities Demonstrated¶
The demo builds through four levels of analytical sophistication:
| Act | Level | Graphs | Key Capabilities |
|---|---|---|---|
| 1 | "It Understands" | 1 | Semantic search, multilingual bridging, entity resolution, temporal extraction |
| 2 | "It Navigates" | 1 | + Schema awareness, Cypher analytics, graph traversal, chained workflows, ontology decoding |
| 3 | "It Connects" | 3 | + Cross-graph entity resolution, multi-graph aggregation, regulatory lifecycle tracing |
| 4 | "It Thinks Like an Analyst" | 3 + ontology | + ECCAIRS code decoding, effectiveness validation, gap analysis, predictive risk identification, temporal pattern estimation, manufacturer-centric intelligence |
The Progression¶
Act 1: "Find me something"
↓
Act 2: "Compute this for me"
↓
Act 3: "Connect these domains"
↓
Act 4: "Think like a safety analyst"
Full Capability Matrix¶
| Capability | Description | First Demonstrated |
|---|---|---|
| Semantic understanding | Interpreting queries that don't match stored labels | Act 1 |
| Multilingual support | Querying and answering across languages | Act 1 |
| Entity resolution | Resolving naming variations across entities | Act 1 |
| Multi-hop traversal | Following relationship chains across entities | Act 1 |
| Temporal reasoning | Extracting and computing time-based information | Act 1 |
| Natural language generation | Synthesizing coherent answers from graph facts | Act 1 |
| Schema awareness | Discovering graph structure before querying | Act 2 |
| Cypher analytics | Aggregation, counting, pattern matching | Act 2 |
| Graph traversal | Multi-depth exploration of entity neighborhoods | Act 2 |
| Chained workflows | Composing multiple tools for a single answer | Act 2 |
| Embedded ontology access | Decoding domain terminology at query time | Act 2 |
| Cross-graph reasoning | Correlating entities across independent graphs | Act 3 |
| Multi-graph aggregation | Computing analytics across multiple domains | Act 3 |
| Regulatory lifecycle tracing | Incident → recommendation → directive chains | Act 3 |
| ECCAIRS code decoding | Translating aviation shorthand to search terms | Act 4 |
| Effectiveness validation | Assessing whether directives prevented incidents | Act 4 |
| Gap analysis | Identifying missing regulatory coverage | Act 4 |
| Predictive risk identification | Finding emerging risks before they become directives | Act 4 |
| Temporal pattern estimation | Projecting regulatory timelines from historical patterns | Act 4 |
| Manufacturer-centric intelligence | Building consolidated risk profiles across all domains | Act 4 |
| Risk prioritization | Combining multi-graph signals to recommend operator actions | Act 4 |
What Just Happened
Thirteen questions, three knowledge graphs, one ECCAIRS ontology, and a single conversation. The final questions — predictive gap analysis and manufacturer intelligence — are the kind of analysis that prevents accidents. They require systematic cross-referencing of incident data against two regulatory databases, with domain knowledge to match failure modes across different naming conventions. This normally takes a senior safety analyst days of manual work across ECCAIRS, the EASA SR database, and the EASA AD database. Aletheia did it in a single conversation.